 A new attack called Pixnapping can steal sensitive data from Android devices, without needing a single permission. The exploit targets visual data on-screen, including two-factor authentication codes, private messages, and location histories. It works by quietly measuring how long it takes to render specific pixels. If that sounds like science fiction, it’s not. Researchers have already tested it on Pixel and Samsung devices with unsettling results. [Read more…]
A new attack called Pixnapping can steal sensitive data from Android devices, without needing a single permission. The exploit targets visual data on-screen, including two-factor authentication codes, private messages, and location histories. It works by quietly measuring how long it takes to render specific pixels. If that sounds like science fiction, it’s not. Researchers have already tested it on Pixel and Samsung devices with unsettling results. [Read more…]
Windows 10 Is Dead. Long Live Windows 10!
 After nearly a decade, Microsoft is finally closing the book on Windows 10. As of today, free support and regular security patches have officially ended. But despite the headlines, your computer is not about to implode. If you plan wisely, or even just use decent security software, you can keep running Windows 10 safely for a quite a bit longer. [Read more…]
After nearly a decade, Microsoft is finally closing the book on Windows 10. As of today, free support and regular security patches have officially ended. But despite the headlines, your computer is not about to implode. If you plan wisely, or even just use decent security software, you can keep running Windows 10 safely for a quite a bit longer. [Read more…]
Malicious CAPTCHA Redirects Turn WordPress Sites into Malware Launchpads
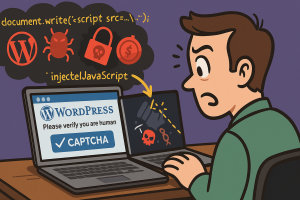 A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
Researchers from Israel’s National Digital Agency revealed that ShadowCaptcha merges social engineering with living-off-the-land tactics. Attackers aim to steal credentials, exfiltrate browser information, deploy cryptomining software, or trigger ransomware—depending on the route the victim takes. [Read more…]
Federal Court Cyberattacks Are a National Security Crisis, Wyden Warns
 Cyberattacks on U.S. federal courts are no longer just IT problems. They now pose a national security threat.
Cyberattacks on U.S. federal courts are no longer just IT problems. They now pose a national security threat.
That is Senator Ron Wyden’s warning in a blunt letter to Chief Justice John Roberts this week, urging the Supreme Court to address repeated breaches of the judiciary’s document filing and email systems. Wyden called the hacks “unacceptable” and said weak practices have left the courts “an inviting target” for foreign adversaries. [Read more…]
Hackers Hide Malware in DNS Records to Evade Detection
 A new cybersecurity threat is emerging as attackers use DNS records—the very system that directs internet traffic—to hide malware. Instead of relying on email attachments or suspicious downloads, bad actors are embedding malicious payloads into DNS TXT records. This method sneaks malicious code past traditional defenses because security tools often ignore DNS traffic.
A new cybersecurity threat is emerging as attackers use DNS records—the very system that directs internet traffic—to hide malware. Instead of relying on email attachments or suspicious downloads, bad actors are embedding malicious payloads into DNS TXT records. This method sneaks malicious code past traditional defenses because security tools often ignore DNS traffic.
DNS, or Domain Name System, acts like the internet’s phonebook, translating domain names into IP addresses. It is so fundamental and routine that most security systems allow it without scrutiny. That makes it a perfect hiding place. According to researchers at Infoblox, attackers are disguising shellcode—malicious binary instructions—inside base64-encoded TXT records. These look like harmless text but are reassembled and executed by compromised devices once fetched. [Read more…]