 We’ve spent the last few years watching language models get disturbingly good at sounding smart. They write coherent essays, debug code, explain quantum physics in simple terms. The experience is convincing enough that serious people have started talking about these systems as if they’re on the cusp of real intelligence, or already past it.
We’ve spent the last few years watching language models get disturbingly good at sounding smart. They write coherent essays, debug code, explain quantum physics in simple terms. The experience is convincing enough that serious people have started talking about these systems as if they’re on the cusp of real intelligence, or already past it.
They’re not. And the gap matters more than the hype suggests.
Look, I get the appeal. When ChatGPT solves a tricky programming problem or writes a passable legal brief, it feels intelligent. But fluency isn’t understanding, and being really good at predicting the next word isn’t the same as knowing how the world actually works. [Read more…]
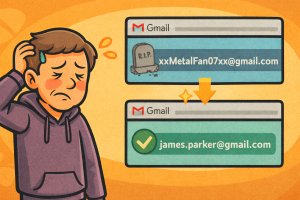 Google is finally undoing one of Gmail’s longest standing frustrations. Users who have been stuck for years with outdated or embarrassing email addresses now have a way out that does not involve starting over. A newly updated Google support document confirms that Gmail accounts can now be assigned a new address while keeping the same account, inbox, and data intact.
Google is finally undoing one of Gmail’s longest standing frustrations. Users who have been stuck for years with outdated or embarrassing email addresses now have a way out that does not involve starting over. A newly updated Google support document confirms that Gmail accounts can now be assigned a new address while keeping the same account, inbox, and data intact.  Microsoft has closed the door on one of the most widely used tricks for activating Windows 11 without paying for it. The company pushed out new security updates this month that permanently disable a set of PowerShell scripts known as MAS, short for Microsoft Activation Scripts. The tools, created by a group called Massgrave, had been circulating on GitHub for years and gave users a quick way to unlock Windows or Office without a valid license.
Microsoft has closed the door on one of the most widely used tricks for activating Windows 11 without paying for it. The company pushed out new security updates this month that permanently disable a set of PowerShell scripts known as MAS, short for Microsoft Activation Scripts. The tools, created by a group called Massgrave, had been circulating on GitHub for years and gave users a quick way to unlock Windows or Office without a valid license.  Apple has launched a new feature that lets U.S. passport holders add their passport as a Digital ID in Apple Wallet, usable at over 250 TSA airport checkpoints nationwide. The rollout marks a key expansion of Apple’s digital identity push and eliminates the need for a physical driver’s license or state ID, at least for domestic travel.
Apple has launched a new feature that lets U.S. passport holders add their passport as a Digital ID in Apple Wallet, usable at over 250 TSA airport checkpoints nationwide. The rollout marks a key expansion of Apple’s digital identity push and eliminates the need for a physical driver’s license or state ID, at least for domestic travel.  On October 20th, 2025, a disruption in a single AWS service rippled through the backbone of the internet. What started as elevated error rates in Amazon’s DynamoDB service in the US-EAST-1 region quickly escalated into a full-blown outage across dozens of AWS products. For anyone who relies on Amazon Web Services, and that’s nearly everyone, this was a stark reminder of just how fragile cloud infrastructure can be.
On October 20th, 2025, a disruption in a single AWS service rippled through the backbone of the internet. What started as elevated error rates in Amazon’s DynamoDB service in the US-EAST-1 region quickly escalated into a full-blown outage across dozens of AWS products. For anyone who relies on Amazon Web Services, and that’s nearly everyone, this was a stark reminder of just how fragile cloud infrastructure can be.