 After nearly a decade, Microsoft is finally closing the book on Windows 10. As of today, free support and regular security patches have officially ended. But despite the headlines, your computer is not about to implode. If you plan wisely, or even just use decent security software, you can keep running Windows 10 safely for a quite a bit longer. [Read more…]
After nearly a decade, Microsoft is finally closing the book on Windows 10. As of today, free support and regular security patches have officially ended. But despite the headlines, your computer is not about to implode. If you plan wisely, or even just use decent security software, you can keep running Windows 10 safely for a quite a bit longer. [Read more…]
12 Rogue Certificates for Cloudflare’s DNS Raise Global Security Alarm
 On Wednesday, researchers uncovered three improperly issued TLS certificates for Cloudflare’s 1.1.1.1 DNS service, encrypted DNS lookup used by millions. The concern was clear: anyone with those credentials could impersonate Cloudflare’s resolver, decrypt user traffic, or redirect queries to malicious sites.
On Wednesday, researchers uncovered three improperly issued TLS certificates for Cloudflare’s 1.1.1.1 DNS service, encrypted DNS lookup used by millions. The concern was clear: anyone with those credentials could impersonate Cloudflare’s resolver, decrypt user traffic, or redirect queries to malicious sites.
Further investigation revealed the breach was worse than initially thought. Cloudflare confirmed that Fina CA—a Microsoft‑trusted certificate authority, had in fact issued a total of twelve unauthorized certificates for 1.1.1.1 since February 2024. [Read more…]
Malicious CAPTCHA Redirects Turn WordPress Sites into Malware Launchpads
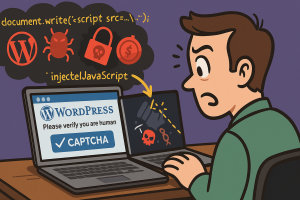 A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
Researchers from Israel’s National Digital Agency revealed that ShadowCaptcha merges social engineering with living-off-the-land tactics. Attackers aim to steal credentials, exfiltrate browser information, deploy cryptomining software, or trigger ransomware—depending on the route the victim takes. [Read more…]
Federal Court Cyberattacks Are a National Security Crisis, Wyden Warns
 Cyberattacks on U.S. federal courts are no longer just IT problems. They now pose a national security threat.
Cyberattacks on U.S. federal courts are no longer just IT problems. They now pose a national security threat.
That is Senator Ron Wyden’s warning in a blunt letter to Chief Justice John Roberts this week, urging the Supreme Court to address repeated breaches of the judiciary’s document filing and email systems. Wyden called the hacks “unacceptable” and said weak practices have left the courts “an inviting target” for foreign adversaries. [Read more…]
When Hidden AI Meets Quantum Doom: The New Enterprise Security Crossroads
 Why Shadow AI Slips Past Security
Why Shadow AI Slips Past Security
Shadow AI is already inside. The tools sit in browsers and sidebars. Employees paste snippets of code, customer notes, even legal language into chatbots that were never vetted. The answers look helpful. The risk hides in the copy and paste. Data leaves the building without a ticket. Logs do not show it. Policies never saw it. By the time a leak becomes visible, the trail is cold.
IT leaders keep asking the same question. How do you govern what you cannot see? You start by naming it. Shadow AI covers any AI use that bypasses purchase, security review, or monitoring. That includes SaaS chat tools, browser extensions, model endpoints wired into internal scripts, and clever “personal assistants” someone installed on a work laptop. Each of those entry points can move sensitive information to third parties. Some keep prompts. Others store outputs. Many train on uploaded files. You cannot make a clean audit if you do not control any of that. [Read more…]
 Why Shadow AI Slips Past Security
Why Shadow AI Slips Past Security