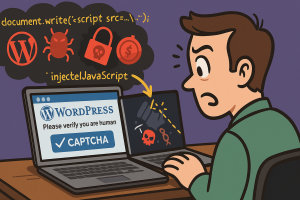
 A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
A sinister campaign known as ShadowCaptcha is using over 100 compromised WordPress sites as unwitting hosts, redirecting visitors to fake CAPTCHA pages. These deceptive pages trigger malware delivery ranging from credential stealers to ransomware and cryptocurrency miners.
Researchers from Israel’s National Digital Agency revealed that ShadowCaptcha merges social engineering with living-off-the-land tactics. Attackers aim to steal credentials, exfiltrate browser information, deploy cryptomining software, or trigger ransomware—depending on the route the victim takes.
The Attack Path
Visitors to infected WordPress sites get redirected via injected JavaScript to counterfeit Cloudflare or Google CAPTCHA screens. A deceptive prompt involving “ClickFix” appears next, guiding users down one of two malicious routes:
- Route 1: Uses the Windows Run dialog to deploy Lumma and Rhadamanthys infostealers via MSI installers or HTA payloads executed with
mshta.exe. - Route 2: Instructs users to save and run an HTML Application (HTA) file manually, which then installs Epsilon Red ransomware.
Tricks, Evasions, and Stealth
ShadowCaptcha is designed to evade detection. It employs anti-debugger code to block browser developer tools, uses DLL side-loading to disguise malware as legitimate processes, and copies malicious commands to the clipboard using navigator.clipboard.writeText, tricking users into pasting them blindly.
Some variants also install XMRig cryptocurrency miners, with dynamic configuration pulled from Pastebin. In some cases, the malware drops a driver named WinRing0x64.sys to gain kernel-level access and increase mining efficiency.
Who’s Being Targeted?
The compromised WordPress sites span Australia, Brazil, Italy, Canada, Colombia, and Israel. Impacted industries include technology, hospitality, finance, healthcare, and real estate.
While exact infection vectors are still being studied, researchers believe the attackers are exploiting vulnerable plugins or logging in using stolen administrator credentials.
Meet the Help TDS Ecosystem
ShadowCaptcha links to a larger malware-as-a-service framework known as Help TDS, which has operated since at least 2017. Help TDS provides attackers with PHP templates that inject malicious code into WordPress sites, often leading to tech support scams and fraudulent landing pages.
At the center of this infrastructure is a malicious plugin named woocommerce_inputs, disguised as a WooCommerce extension. It’s now believed to be installed on over 10,000 sites worldwide. The plugin conducts credential harvesting, enforces geo-targeting, hides its presence, and supports remote updates through built-in C2 logic.
Why This Matters
ShadowCaptcha isn’t just another malware campaign—it’s a signal that cybercrime is evolving. By combining deceptive UI elements, legitimate Windows tools, and modular malware kits, attackers are able to shift tactics fluidly. Whether they’re after passwords, computing power, or ransom payouts depends on what makes the most money in the moment.
What You Can Do
- Train users to treat CAPTCHA pages with caution, even those with familiar branding.
- Enable multi-factor authentication (MFA) on all WordPress admin accounts.
- Audit plugins regularly, especially for fakes posing as WooCommerce extensions.
- Segment your network to limit damage from breaches and prevent lateral movement.
- Monitor for indicators of compromise such as unknown database entries or scheduled tasks.
- Maintain regular offline backups and monitor site integrity.
- Deploy intrusion detection systems (IDS) or web application firewalls (WAFs) to catch redirect attempts.
As attacks like ShadowCaptcha become more sophisticated, security hygiene isn’t optional—it’s survival.